78% of OT Incidents Start With a Phishing Email
Energy is the second most targeted sector in the world. Manufacturing, utilities, and defense facilities are under daily attack from nation-state actors — and the entry point is almost always a phishing email sent to a human employee. Jericho Security closes that gap with AI-powered cybersecurity training built for industrial environments.

What does Jericho's
OT Security training cover?
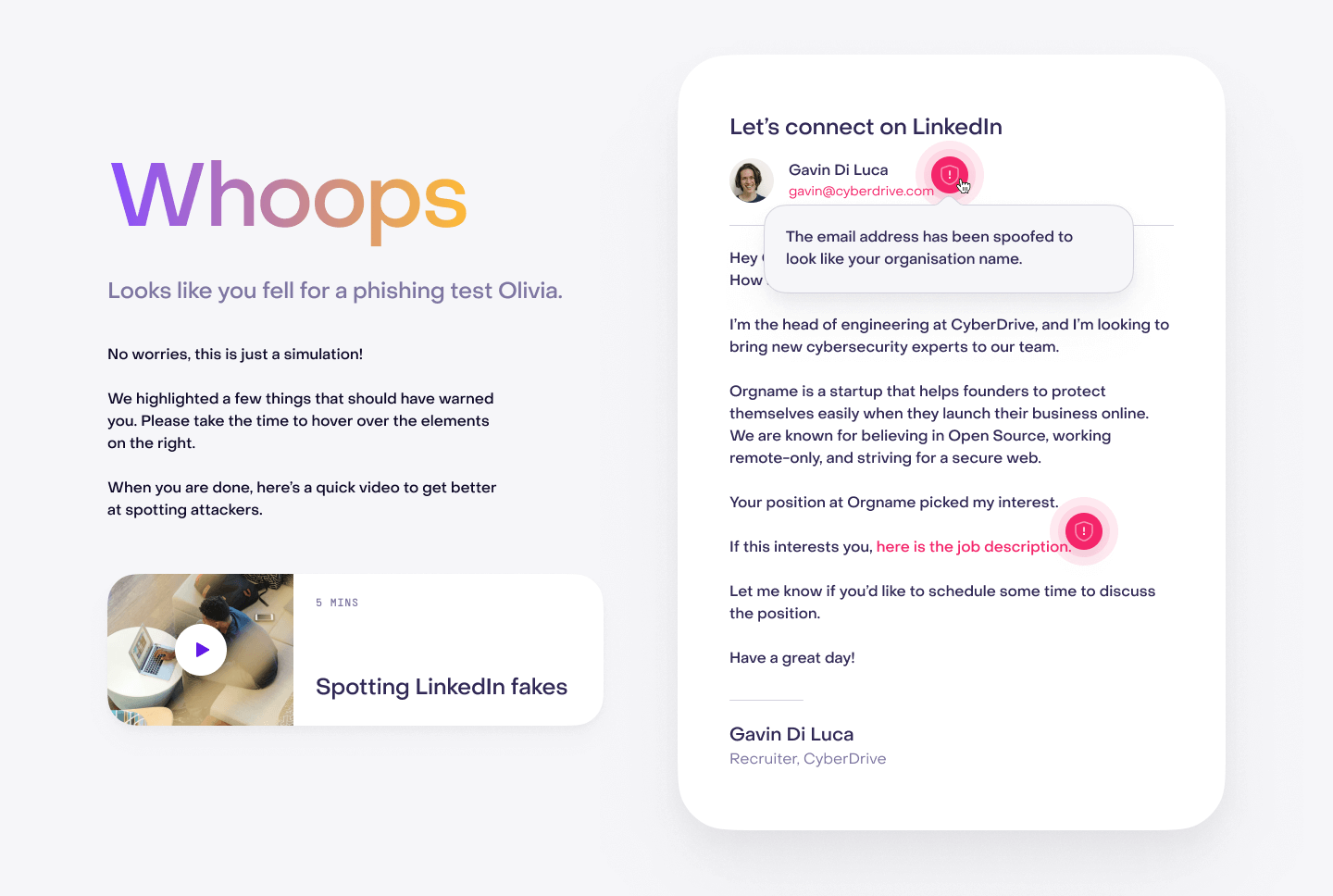
OT-Specific Phishing Simulations
Jericho builds phishing simulations tailored to OT and industrial environments — vendor impersonation, HMI software update lures, SCADA access requests, and emergency maintenance pretexts. Employees in plant operations, engineering, and facilities management train against the exact scenarios attackers use to target their roles.
"Generic phishing training wasn't cutting it for our plant floor staff. Jericho's OT-specific scenarios changed how our team thinks about email security entirely." – CISO, Energy Utility


NERC CIP & IEC 62443 Compliance Training
Jericho's training modules are designed to satisfy NERC CIP, ISA/IEC 62443, and NIST SP 800-82 requirements for industrial cybersecurity awareness. Track completion, generate audit-ready reports, and demonstrate workforce compliance to regulators — all from a single platform.
"Jericho made NERC CIP compliance training engaging for the first time. Our audit results improved dramatically in the first cycle after deployment." – Compliance Officer, Regional Power Grid


IT/OT Converged Security Awareness
IT/OT network convergence is accelerating — and so is the attack surface. Jericho delivers unified security awareness training that bridges IT and OT teams, ensuring both populations share a common understanding of phishing threats, social engineering tactics, and incident reporting protocols specific to industrial control environments.
"As our IT and OT networks converged, our attack surface doubled. Jericho's converged training program was the only one that addressed both sides of our workforce." – VP of Security, Manufacturing


Nation-State & Critical Infrastructure Threats
Critical infrastructure is a primary target for nation-state adversaries. Jericho's advanced simulation library includes nation-state TTPs — spear-phishing with OT-specific lures, supply chain compromise pretexts, and long-dwell espionage scenarios — giving defense and critical infrastructure teams realistic threat exposure in a controlled environment.
"Jericho's nation-state threat simulations gave our team a realistic sense of what we're actually up against. It's a completely different level than commercial phishing training." – Security Director, Defense Supplier


Why Choose Jericho for OT Security Training?
Critical infrastructure is under sustained attack. Energy, manufacturing, and defense sectors face daily spear-phishing campaigns designed to cross the IT/OT boundary and reach industrial control systems. The consequences of a successful breach go beyond data loss — operational shutdown, physical damage, and national security implications are on the table. Human awareness training is the fastest, most cost-effective defense layer available.
Training Built for OT, Not Retrofitted From IT
Most security awareness training was built for office workers clicking email links. OT environments have fundamentally different threat surfaces, workflows, and risk profiles. Jericho's content is purpose-built for the people who run industrial systems — not adapted from generic IT training.
$1.31M Average Recovery Cost in Energy & Utilities
A single successful phishing attack on an OT network can cause physical damage, operational shutdown, and safety incidents — not just data loss. The average recovery cost in energy and utilities is $1.31M. The business case for prevention is undeniable.
Audit-Ready Compliance Reporting
Jericho's compliance-aligned modules help organizations meet NERC CIP, IEC 62443, NIST 800-82, and DOD CMMC requirements. Automated reporting delivers audit-ready evidence of workforce training completion without manual overhead.
Signs your OT environment is one phishing email away from a breach
Your IT and OT networks are converged
Your IT and OT networks share connectivity — meaning a compromised IT credential can become a pivot point into your industrial control systems. IT/OT convergence without corresponding security training is a critical gap that attackers actively exploit.
You need to meet NERC CIP or IEC 62443 compliance
NERC CIP, IEC 62443, NIST 800-82, and CMMC all require documented cybersecurity awareness training for personnel with access to critical systems. Failure to demonstrate workforce training compliance during audits carries significant financial and operational penalties.
Your OT workforce receives generic IT security training
Your security awareness program was designed for corporate IT users. Plant operators, field engineers, and technicians receive the same generic training — if any at all. These employees are targeted with OT-specific lures that standard training never covers.
Your industrial systems are one phishing email away from shutdown.
78% of OT incidents begin with a phishing email. The average recovery cost in energy and utilities is $1.31M. Jericho Security's OT-specific training closes the human vulnerability gap before it becomes an operational crisis.
OT Cybersecurity Training - FAQs
What is OT cybersecurity?
OT (Operational Technology) cybersecurity refers to protecting the industrial control systems, SCADA systems, PLCs, and physical infrastructure that run manufacturing plants, energy grids, water utilities, and defense facilities. Unlike IT security, OT breaches can cause physical damage and safety incidents in addition to data loss.
Why does OT security training focus on phishing?
Research shows that 78% of OT cybersecurity incidents are initiated through phishing attacks targeting employees. Attackers use OT-specific lures — fake vendor maintenance requests, SCADA software update emails, and engineering portal access phishing — to gain initial access before pivoting into industrial control networks.
How does Jericho's OT security training work?
Jericho delivers phishing simulations and security awareness training specifically designed for OT environments — including scenario libraries built around industrial lures, vendor impersonation, and IT/OT boundary attacks. Training modules are mapped to NERC CIP, IEC 62443, and NIST 800-82 frameworks with automated compliance reporting.
Does Jericho's training satisfy NERC CIP compliance requirements?
Yes. Jericho's training modules are mapped to NERC CIP (Critical Infrastructure Protection), ISA/IEC 62443, NIST SP 800-82, and DOD CMMC requirements. Automated reporting generates the documented evidence of workforce training completion required for regulatory audits.
What is the IT/OT convergence security risk?
IT/OT convergence — connecting operational technology networks to corporate IT infrastructure — dramatically expands the attack surface. A compromised IT credential can become a pivot point into industrial control systems. Jericho's converged training ensures both IT staff and OT operators share a unified security posture and incident response awareness.
Which industries need OT cybersecurity training?
Energy, utilities, manufacturing, defense contractors, water treatment, transportation, and any organization with industrial control systems or critical infrastructure. These sectors are consistently the most targeted by nation-state actors and criminal ransomware groups seeking maximum disruption leverage.
Ready to get started?
Industrial environments face a unique threat landscape that generic security training doesn't address. Jericho Security's OT-specific phishing simulations and compliance-aligned training modules give your workforce the tools to stop attacks before they cross the IT/OT boundary. Schedule your free demo today.